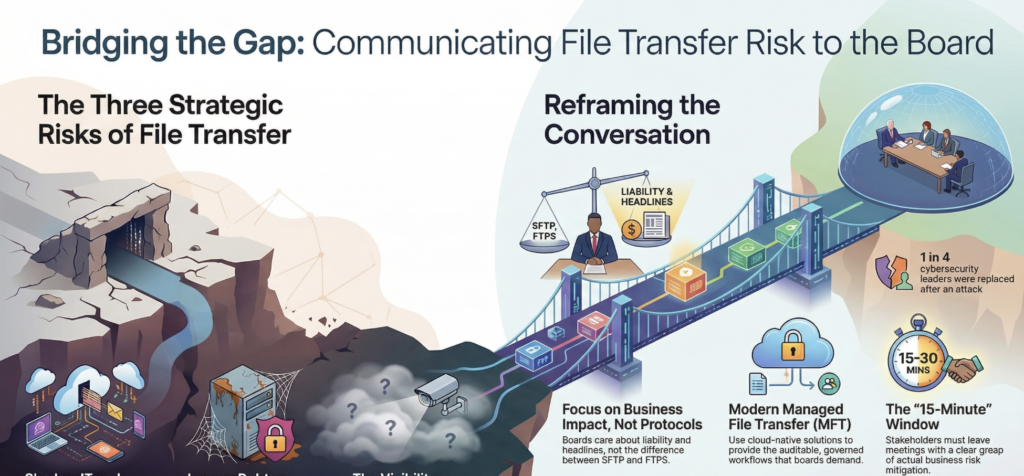
A recent piece in IT Brew got us thinking. Drawing on 2026 benchmark data from IANS Research, the article found that most CISOs get just 15–30 minutes per quarter with their board, and even then, stakeholders often leave without a clear grasp of actual business impact. As one security leader quoted in the piece put it, it’s not a time problem. It’s an impact situation. [“CISOs Are Meeting With Board Leaders, But Are They Being Heard?” — IT Brew, March 2026]
If CISOs are struggling to communicate cyber risk to board members in plain business terms, file transfer is one of the most concrete and underexplained examples of where that gap shows up. Here’s how we’d frame that conversation.
The Board Isn’t Asking About Protocols
When board members think about cybersecurity risk, they’re not thinking about SFTP vs. FTPS. They’re thinking about headlines, liability, and operational disruption. They want to know: Could this happen to us? How bad would it be? Are we covered?
Your job isn’t to walk them through your transfer architecture. It’s to answer those three questions — clearly, in terms they recognize.
Here’s how to frame the file transfer conversation in language that lands.
Risk #1: Sensitive Data Moving Through Channels You Don’t Control
When employees can’t easily move files through approved systems — because those systems are slow, clunky, or hard to access — they find workarounds. Email attachments. Consumer file-sharing tools. Personal cloud storage. It happens in every organization, and most IT teams know it.
For the board, the question isn’t “do employees use unauthorized tools?” The question is: What’s the exposure when they do?
The answer: uncontrolled data movement means you may have no record of what was left in the organization, when, or to whom. In a regulated industry — healthcare, financial services, government contracting — that’s not just a security problem. It’s a compliance and legal liability problem. HIPAA, PCI-DSS, CMMC, and similar frameworks all require demonstrable controls over sensitive data in transit.
What boards want to hear: “We have governed transfer workflows that keep sensitive data on approved, audited infrastructure — and we have the logs to prove it.”
Risk #2: Legacy Transfer Infrastructure as an Open Attack Surface
Many organizations are still running file-transfer environments set up years ago — sometimes decades ago. Old FTP servers. Homegrown SFTP configurations. Transfer processes bolted onto aging on-premises infrastructure that hasn’t been patched or reviewed in years.
These aren’t just operational liabilities. They’re active security risks. Unpatched servers are well-documented entry points for attackers. IT Brew cited a 2025 Sophos report finding that one in four cybersecurity leaders were replaced following a ransomware attack — a sobering reminder that the consequences of an incident reach well beyond the technical team.
In many of those incidents, initial access wasn’t sophisticated. It was a forgotten, exposed service that nobody was watching.
What boards want to hear: “Our transfer infrastructure is cloud-native, actively maintained, and not carrying technical debt that creates unnecessary attack surface.”
Risk #3: No Audit Trail Means No Defense
In the event of a breach, an audit, or a regulatory inquiry, one of the first things investigators ask for is evidence: who transferred what, when, and where it went? If your file transfer environment can’t produce that evidence cleanly, the absence itself becomes a problem.
This matters for board-level risk in a specific way: it affects how liability is assessed and how quickly an incident can be contained and explained. Organizations that can reconstruct a clean chain of custody for data movement are in a fundamentally different position than those that cannot.
What boards want to hear: “Every transfer is logged, auditable, and traceable to a specific user, timestamp, and destination.”
Turning Controls Into a Conversation
The goal isn’t to make your board into file transfer experts. It’s to give them the confidence that the risk has been identified, translated into business terms, and addressed with appropriate controls.
Modern managed file transfer solutions — purpose-built for cloud environments, with centralized access controls, complete audit logging, and direct integration with cloud storage services such as AWS S3, Azure Blob Storage, and Google Cloud Storage — exist precisely to close these gaps. They replace ad-hoc, hard-to-govern transfer processes with something auditable, scalable, and defensible.
When you walk into that 15-minute window, that’s the story worth telling: not the technology, but the risk it mitigates — and the business continuity, compliance standing, and liability protection that comes with getting it right.
Want to see how Thorn Technologies approaches cloud-native file transfer security? Explore SFTP Gateway and StorageLink, built for enterprise environments where auditability and control aren’t optional.